News
Hackers Can Fool Radiologists and AI Software by Manipulating Lung Cancer Scans
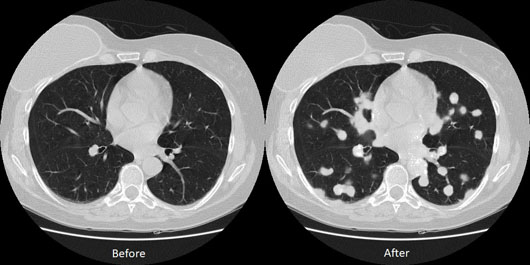
Hackers can access a patient’s 3D medical scans to add or remove malignant lung cancer and deceive both radiologists and AI algorithms that are used to aid diagnosis, according to a new study published by Ben-Gurion University (BGU) of the Negev cybersecurity researchers. Click here for a video of the attack.
A 3D CT scan combines a series of X-ray images taken from different angles around the body and uses computer processing to create cross-sectional slices of the bones, blood vessels, and soft tissues. CT images provide more detailed information than standard X-rays and are used to diagnose cancer, heart disease, infectious diseases, and more. An MRI scan is similar, but uses powerful magnetic fields instead of ionizing radiation to diagnose bone, joint, ligament, and cartilage conditions.
Malicious attackers can tamper with the scans to deliberately cause a misdiagnosis for insurance fraud, ransomware, cyberterrorism, or even murder. Attackers can even automate the entire process in a malware that can infect a hospital’s network.
“Our research shows how an attacker can realistically add or remove medical conditions from CT and MRI scans,” says Yisroel Mirsky, PhD, lead researcher in the BGU department of software and information systems engineering and project manager and cybersecurity researcher at BGU’s National Cyber Security Research Center. “In particular, we show how easily an attacker can access a hospital’s network and then inject or remove lung cancers from a patient’s CT scan.”
The attacker has full control over the number, size, and locations of the cancers while preserving the same anatomy from the original, full-resolution 3D image. This is a significant threat since 3D medical scans are considered to provide more definitive evidence than preliminary 2D X-rays. To demonstrate the feasibility of the attack, with permission, the researchers broke into the network of an actual hospital and intercepted every scan taken by a CT scanner.
“The scans were not encrypted because the internal network is usually not connected to the internet. However, determined intruders can still gain access via the hospital’s Wi-Fi or physical access to the infrastructure,” Mirsky says. “However, these networks are now being connected to the internet as well, which enables attackers to perform remote attacks.”
To inject and remove medical conditions, the researchers used a deep learning neural network called a generative adversarial network (GAN). GANs have been used in the past to generate realistic imagery, such as portraits of nonexistent people. The researchers showed how a 3D conditional GAN can be used to efficiently manipulate high resolution 3D medical imagery. The architecture (CT-GAN) uses two of these GANs: one trained to inject cancer and the other trained to remove cancer.
The BGU researchers verified the attack effectiveness by training CT-GAN to inject or remove lung cancer using free medical imagery from the internet. They hired three radiologists to diagnose a mix of 70 tampered and 30 authentic CT scans.
When the scans of healthy patients were injected with cancer, the radiologists misdiagnosed 99% of them as being malignant. When the algorithm removed cancers from actual cancer patients, the radiologists misdiagnosed 94% of the patients as being healthy. After informing the radiologists of the attack, they still could not differentiate between the tampered and authentic images, misdiagnosing 60% of images with injections and 87% of those with removals.
“In addition to the radiologists, we also showed how CT-GAN is an effective adversarial machine learning attack,” Mirsky says. “Consequently, the state-of-the-art artificial intelligence lung cancer screening tools, used by some radiologists, are also vulnerable to this attack.”
The researchers proposed some immediate countermeasures that can mitigate most of the threat. One solution is to enable encryption between the hosts in the hospital’s radiology network. In addition, some hospitals can enable digital signatures so that their scanners sign each scan with a secure mark of authenticity. If this approach is followed, administrators should then ensure that proper signatures are being used and that the end devices are correctly verifying these signatures.
“Another method for testing the integrity of the images is to perform digital watermarking (DW), the process of adding a hidden signal into the image such that tampering corrupts the signal and thus indicates a loss of integrity,” Mirsky says. “Unfortunately, the vast majority of medical devices and products currently do not implement DW techniques.”
— Source: Ben-Gurion University of the Negev; Image courtesy of Ben-Gurion University of the Negev
